Related Jobs
View all jobsMalware Analyst
Cyber Security Analyst
SOC Analyst
Vulnerability Analyst
Cyber Security Analyst
Subscribe to Future Tech Insights for the latest jobs & insights, direct to your inbox.
Industry Insights
Discover insightful articles, industry insights, expert tips, and curated resources.

Cyber Security Jobs for Career Switchers in Their 30s, 40s & 50s (UK Reality Check)
If you’re thinking about switching into cyber security in your 30s, 40s or 50s, you’re in good company. Across the UK, organisations of all sizes are hiring people from diverse backgrounds to protect systems, data & customers. But with hype around “hackers” & quick-win courses, it’s hard to separate reality from fiction. This guide gives you a UK reality check: which roles genuinely exist, what employers actually want, how training really works, what to expect on salary & progression & whether age matters. Whether you come from finance, project management, operations, law, HR or customer service, there is a credible route into cyber security if you approach it strategically.

How to Write a Cyber Security Job Ad That Attracts the Right People
Cyber security is now a board-level priority for organisations across the UK. From financial services and healthcare to critical infrastructure, SaaS platforms and the public sector, demand for skilled cyber security professionals continues to grow. Yet despite this demand, many employers struggle to attract the right candidates. Cyber security job adverts often generate large volumes of applications, but few are a genuine match. Meanwhile, experienced security engineers, analysts and architects quietly ignore adverts that feel vague, unrealistic or disconnected from real security work. In most cases, the problem is not a lack of talent — it is the quality of the job advert. Cyber security professionals are trained to assess risk, spot weaknesses and question assumptions. A poorly written job ad signals organisational immaturity and weak security culture. A well-written one signals seriousness, competence and trust. This guide explains how to write a cyber security job ad that attracts the right people, improves applicant quality and positions your organisation as a credible security employer.
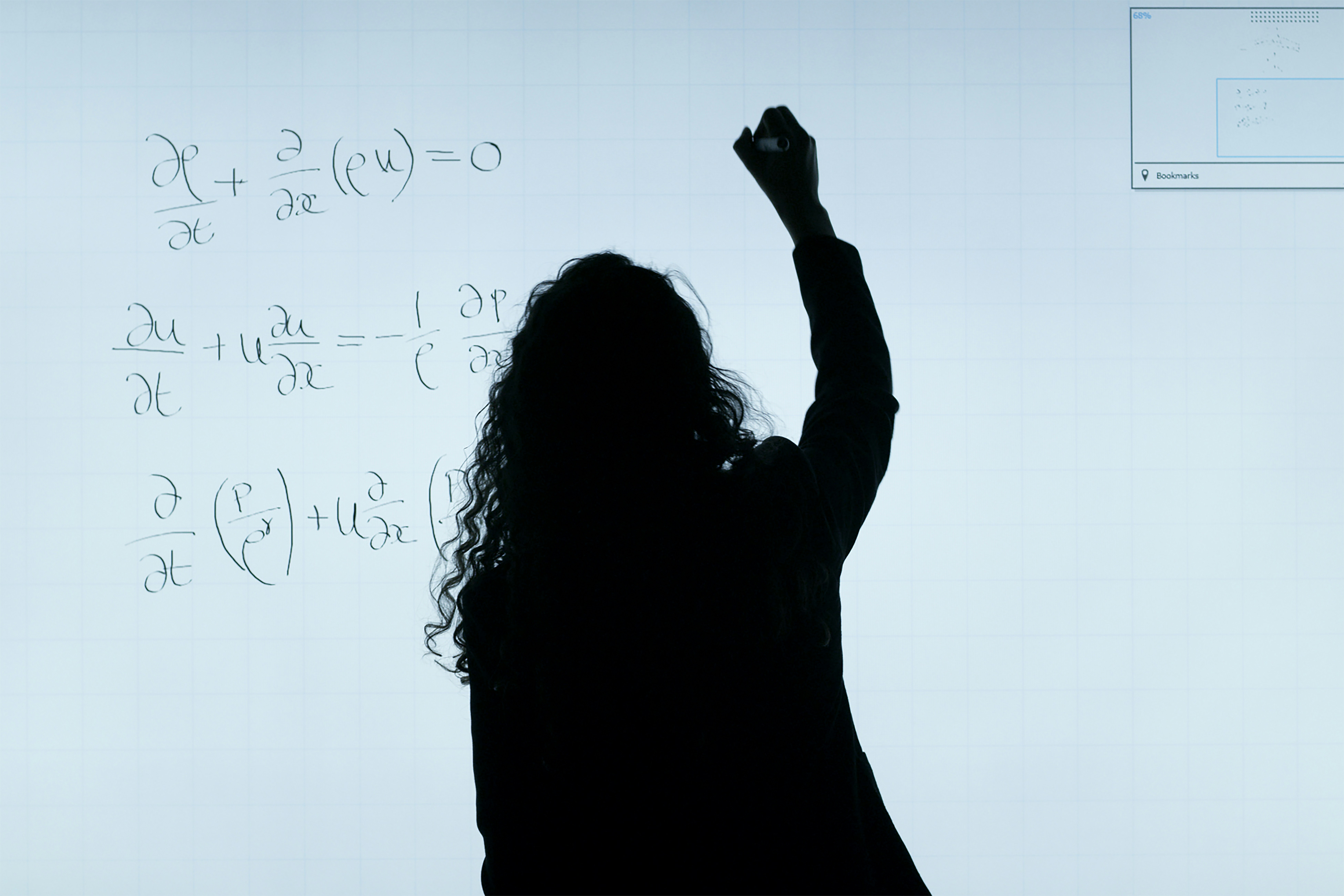
Maths for Cyber Security Jobs: The Only Topics You Actually Need (& How to Learn Them)
If you are applying for cyber security jobs in the UK it can feel like “real security people” must be brilliant at maths. The reality is simpler: most roles do not need degree-level pure maths. What they do need is confidence with a small set of practical topics that show up repeatedly in day-to-day work across SOC, incident response, cloud security, AppSec, threat detection, IAM & security engineering. This guide strips the maths down to what actually helps you get hired. It includes a 6-week learning plan plus portfolio projects you can publish to prove the skills. You will focus on: Number systems & bitwise thinking (binary, hex, bytes, XOR) Modular arithmetic basics (enough to understand how modern crypto “works”) Probability & statistics for detection, triage & risk Discrete maths for logic, sets, graphs & complexity Security maths habits: estimation, false positive control & evidence-led reporting You will not waste time on heavy theory that rarely appears in junior or mid-level cyber security roles.